Cyberattack traced to hacked refrigerator
chac_mool
10 years ago
Related Stories

HOUZZ TOURSHouzz Tour: Visit a Modern Update in Oakland
See how a "hacked together" home became an urban neighborhood jewel
Full Story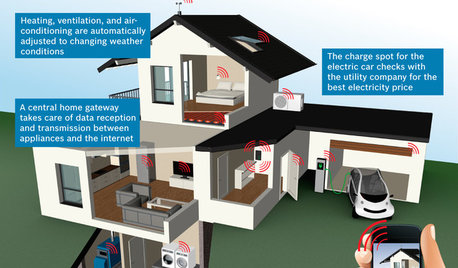
THE HARDWORKING HOMECES 2015: Inching Toward a Smarter Home
Companies are betting big on connected devices in 2015. Here’s a look at what’s to come
Full Story
MATERIALSAre You a Maker? Show Us Your Favorite Tool or Material
Houzz Call: A tool or material can be a maker’s best friend. We’d like to see your favorite — and what it helps you achieve
Full Story
KITCHEN COUNTERTOPSKitchen Counters: Granite, Still a Go-to Surface Choice
Every slab of this natural stone is one of a kind — but there are things to watch for while you're admiring its unique beauty
Full Story
KITCHEN CABINETSChoosing New Cabinets? Here’s What to Know Before You Shop
Get the scoop on kitchen and bathroom cabinet materials and construction methods to understand your options
Full Story
DIY PROJECTS20 Wonderfully Inventive DIY Projects by Houzzers
You'll never look at a wood scrap or empty jar the same way again. Borrow these ideas or just let them inspire your own project
Full Story






Gooster
bmorepanic
Related Professionals
Haslett Kitchen & Bathroom Designers · Pleasant Grove Kitchen & Bathroom Designers · Ridgefield Kitchen & Bathroom Designers · Ridgewood Kitchen & Bathroom Designers · Schenectady Kitchen & Bathroom Designers · North Druid Hills Kitchen & Bathroom Remodelers · Bellevue Kitchen & Bathroom Remodelers · Blasdell Kitchen & Bathroom Remodelers · Hunters Creek Kitchen & Bathroom Remodelers · Lomita Kitchen & Bathroom Remodelers · Oxon Hill Kitchen & Bathroom Remodelers · Rancho Cordova Kitchen & Bathroom Remodelers · Southampton Kitchen & Bathroom Remodelers · Walnut Creek Kitchen & Bathroom Remodelers · Cranford Cabinets & CabinetryGooster